
The whole of science is nothing more than a refinement of everyday thinking.
Albert Einstein, “Physics and Reality”, Journal of the Franklin Institute, 1936
The body of this book argued that the architecture is what matters. This appendix is for the reader who closed the last chapter and asked: could I build this?
What follows is not the book in a different register. It is the load-bearing skeleton pulled out of the narrative chapters and set down next to it in engineering register. The prose chapters remain the primary argument. The appendix is the spec a builder would read on a second pass, with the narrative still in mind.
Three ground rules carry from the Fingerprint chapter into these pages. One: the present tense here is conditional. This is a sketch, not a report on a system that exists. Two: the primitives are established technology. Proof of work, hash chains, public-key signatures, Merkle trees, timestamping services. Nothing in this appendix requires new cryptography. Three: what is mine is the stack, not the pieces. Any engineer who reads this and decides to build is welcome to the stack. They should feel free to change everything in it except the properties in §1.
§1 Properties the substrate must carry
The Tree of Proof does not prescribe a specific Layer. It prescribes properties. A substrate that carries all of the following is a candidate. A substrate that carries only some of them is not.
- Persistence. Once committed, the record cannot be unilaterally deleted. The cost of rewriting the record grows monotonically with time.
- Verifiability without a referee. Any party with the public inputs can verify the record themselves. No trusted third party is required in the verification path.
- Source binding. Each committed observation is tied to a cryptographic identity, a public key, that cannot be reset, re-issued, or laundered by an administrator.
- Selective disclosure. The observation itself need not sit on chain. A commitment to the observation (a hash) does. The full datum can be revealed to the parties who need it and checked against the commitment.
- Space for counter-commitment. A party that disagrees with a committed observation can commit their disagreement in the same substrate, at comparable cost, under their own key.
- Visible falling. When the datum behind a commitment no longer matches the commitment, the branch falls in a way that is observable to anyone reading the substrate.
Bitcoin L1 satisfies persistence and verifiability-without-a-referee. Layer 2 protocols and timestamping services (OpenTimestamps, for example) can provide throughput without sacrificing the anchor. Client-side validation stacks can carry selective disclosure. The engineer chooses the composition. The properties are the non-negotiable.
§2 The Fingerprint primitive
The Fingerprint is the atomic unit. Its construction is three lines:
- The observer produces a signed commitment:
sig = Sign(privkey, H(datum || context)), wherecontextbinds the observation to its category, timestamp, and any collection root under which it will be anchored. - The signed commitment is inscribed on the substrate at block height
h, producing a durable anchorA = H(sig || blockhash(h)). - The full
datumlives off chain. A verifier retrievesdatum, recomputesH(datum || context), checks the signature against the claimed public key, and checks thatAappears at heighth.
The branch that results carries two orthogonal guarantees at once. The first is thermodynamic. Cost burned to place the anchor, cost required to erase it. The second is cryptographic. The identity that stood behind the observation, verifiable against the public key without any referee in the loop.
On-chain bytes are minimal. The inscription is a hash. The full observation lives wherever the observer chooses to publish it, under whatever privacy constraints are appropriate to that datum. What the substrate carries is not the conversation. It carries the undeniable proof that the conversation happened, tagged, priced, and permanent.
§2a A branch
A branch is a Merkle tree, anchored as an inscription, chained to its history by a digital signature that binds to the specific extension being inscribed.
The chain begins with a genesis inscription containing the branch’s public key and, where the branch is a child of another, the genesis hash of the parent branch it declares itself under. The whole payload is signed by the corresponding private key as proof of possession. The genesis is the only root that does not point backward in its own history. There is no previous root to point to. The parent reference, where present, is a different kind of pointer: outward to another branch, not backward to a prior root of this one.
Every subsequent root is constructed in three steps:
- The operator assembles the leaves intended for the new root and computes a pre-image root:
R_pre_n = MerkleRoot(intended_leaves). - The operator signs over the pre-image root, the previous root, and their own public key:
sig_n = Sign(privkey, H(R_pre_n || R_{n-1} || pubkey)). - The signature is added to the leaf set, by convention, as the rightmost leaf, and the inscribed root is recomputed:
R_n = MerkleRoot(intended_leaves ∪ {sig_n}). R_n is what gets anchored on the substrate.
The verifier inverts the construction. Reading R_n off the chain, they identify the rightmost leaf as sig_n, remove it, recompute R_pre_n from the remaining leaves, compute H(R_pre_n || R_{n-1} || pubkey) independently, and verify sig_n against pubkey over that hash. They then walk backward to R_{n-1} and verify the next link the same way, until the chain terminates at the genesis the branch claims.
Continuity of identity across roots is not a convention. It is a chain of signatures, each link anchored to the substrate’s thermodynamic clock, and each signature cryptographically bound to the specific extension it authorizes.
This buys four things, each scoped to what the construction actually delivers.
Branch ownership is explicit, given the genesis declaration, and resettable only by loss of the private key. Not by an administrator.
Each signature binds to a specific extension. The same signature cannot be replayed into a different root, because a different root would compute a different pre-image root, and the signature only verifies over the original. An external party cannot copy the operator’s signature into their own claimed extension; an attacker who tampers with any leaf in R_n breaks R_pre_n and the signature no longer verifies. The owner can still fork their own branch, by deliberately signing a second, distinct extension of R_{n-1}, but each fork is a freshly committed signature, not a copy of an existing one, and the substrate’s clock records which one was inscribed first.
And combined with the consistency proofs in §7, the reader audits provenance end-to-end, identity continuity from this section, content continuity from that one, without trusting any operator’s claim about their own history. The provenance is the substrate, not the brand.
And the parent reference makes branch population bilateral. A category branch claiming a child does not get to declare it; the child’s own genesis must name the parent’s genesis hash, signed under the child’s private key, anchored at the child’s own block height, paid for by the child’s own fee. A parent that lists a thousand children whose genesis inscriptions do not point back has a thousand text references and zero attested children. A parent whose thousand children independently inscribed a parent reference pointing home has a thousand attested children, each with its own four-force history. The structural weight of a category branch is summed from the children’s vectors, not the parent’s claim. Sybil attacks remain possible, an operator who manufactures a thousand sock-puppet children, paying for each genesis inscription, is performing the wealth-bias attack Seam I names, but the fraud has migrated from cardinality to cost, where time decays it the way the manuscript already accepts.
The Fingerprint primitive (§2) signs individual observations. The branch construction signs the structural history of the branch itself. Both addressing layers use the same key. A signed observation under a branch is therefore traceable in two directions: forward to the leaf, and backward through the branch’s signed chain of roots to the genesis the branch was first anchored from.
§2b Branch metadata
A branch that exists structurally (genesis anchored, roots chained, parent attested) is not yet a branch an agent can navigate. The bilateral attestation in §2a tells the agent this branch’s parent is X and its children are Y, Z, …. It does not tell the agent which child to descend into for what query. Without that, an agent reading a category branch with a thousand children has to descend into every one of them to find what it wants. Blind traversal is the failure mode the navigation layer must close.
Two layers of metadata close it. Self-description, published by each branch under its own key, is the authority. Index leaves, published by each parent as a catalog of its children, are the cache. The agent reads the cache to navigate. The agent verifies against the authority when it cares.
Self-description. Each branch publishes a small set of inscribed leaves under its own key, signed and anchored under one of the branch’s roots like any other leaf. A category label declaring what the branch is of, a schema declaring the structure leaves are expected to carry, and optional cross-references to peer branches the operator considers related, competitive, or complementary. Convergence on labels happens the way DNS conventions converged: through use, cross-reference, and cost. A branch whose declared label is contradicted by the leaves it actually publishes is detectable by any reader who walks the leaves. Cross-references the peer reciprocates carry more weight than one-sided ones. The same bilateral attestation pattern that scopes parent-child weight scopes peer relationships too.
Index leaves. A parent branch publishes a structured catalog of its children, refreshed at each of the parent’s anchors. For each child, the index records: the child’s genesis hash (the bilateral attestation pointer), the child’s declared category label copied from the child’s self-description, the child’s four-force vector at the moment the index was last refreshed, and a pointer to the child’s self-description leaf so the agent can verify if it descends. An agent landing at a parent reads the index, matches its query against the children’s labels and weight summaries, selects the child whose topic matches and whose weight justifies the descent, and descends only into the matching child. The remaining children are not walked. A category branch with a thousand children is navigated in log(N) reads, not N reads.
Cache versus authority. The parent’s index is a cache, not an authority. The same discipline §7 holds for the summary object holds here: a lie in the index is mechanically detectable because the underlying chain data is always the authority. If the parent’s index entry for a child says category: oncology and the child’s own self-description says category: cardiology, the agent reads both and the contradiction is on chain. The child’s signed self-description is what the agent trusts. The parent’s index is what the agent reads first because it is faster. An agent in a hurry trusts the cache. An agent in an audit walks the chain.
The four forces apply at both layers. An index leaf with three years of refresh history under a parent that has held weight for a decade is read differently than an index leaf published yesterday under a parent with no anchor history. A self-description signed by a branch with thousands of accurate prior observations is read differently than the same fields signed by a branch with no track record. Old, costly, structurally proximate, hash-valid metadata weighs more than new, cheap, distant, hash-invalid metadata. Navigation inherits the substrate’s honesty at every step.
The agent’s blindness in The Index Problem was that reputation lived outside the surface the agent could read. With self-descriptions anchored under each branch’s own key and index leaves cataloging children at each parent, the surface the agent reads contains both the directory and its provenance. The agent reads the index to find the path. The agent verifies the path against the substrate when it matters. The blind traversal that The Index Problem opened on closes here, in this section, with two leaves and a four-force vector.
§3 The four forces
Every node on the tree is weighted by four independent variables. All four must be present. Remove any one and the node’s weight collapses.
- Time.
t = now - block_time(h). How long has the commitment held? Time can be survived. It cannot be purchased. - Value.
v = fee_paid(h) × difficulty(h). How much thermodynamic work was spent to place the anchor? The economic sacrifice is a filter. - Proximity.
p = distance_from_trunk(node). How structurally close is the node to the tree’s load-bearing core? A primary branch carries more weight than a distant twig with the same words on it. - Hash validity.
hv = (H(datum || context) == committed_hash). Does the off-chain datum still match the on-chain commitment? The only dynamic force. It can flip at any moment.
A node’s weight is not a single scalar the chain computes. It is a four-tuple the reader interprets. Any weighting function, w = f(t, v, p, hv), is the reader’s to choose, to publish, to defend, or to revise. The chain does not score. The reader does. The chain only guarantees that the four variables are what they are.
§4 Collections and the hierarchy of weight
Signing is cheap. Inscribing is not. A Merkle tree solves the asymmetry.
An oracle producing many observations in a window hashes them into a tree, signs the root, and inscribes the signed root. One transaction. The full set is anchored. Each individual observation is verifiable against the root with a logarithmic proof. No individual leaf needed to be buried separately.
What falls out of this, without any governance decision, is a hierarchy that mirrors the importance the oracle assigns to each collection. High-stakes collections are anchored often, with high fees, at positions close to the trunk of the tree. Low-stakes collections are anchored rarely, cheaply, at peripheral positions. The fee market encodes the hierarchy. No one had to declare it.
The engineer’s scaling question has a clean answer: anchor the Merkle roots on L1. Stream the leaves through a relay mesh, a Nostr-shaped network would serve, and batch-anchor the roots at whatever cadence the collection’s stakes justify. OpenTimestamps is the existing reference implementation of the batching pattern.
§5 Legible silence
The active-attendee requirement closes the choice-versus-failure ambiguity that a passive oracle architecture leaves open.
An oracle’s node publishes continuous heartbeats. Low-stakes signatures on routine collections, channel updates if the substrate is Lightning-shaped, pings on public relays. Nothing consequential. Just the proof, block by block, that the public key is online and capable of signing.
In a window where the node is demonstrably alive, the absence of a signature on a specific observation is no longer indistinguishable from a crash. It is a selection. A verifier who reads the substrate can distinguish three states:
SIGNED. The oracle committed.REFUSED. The oracle was present and chose not to commit.ABSENT. The oracle was not present; nothing can be inferred.
The REFUSED state is the one conventional systems cannot express. On this substrate it is a first-class signal. Censorship, disagreement, and cowardice all leave a footprint. The footprint carries the block timestamp, the public key, and the shape of what the oracle chose not to say.
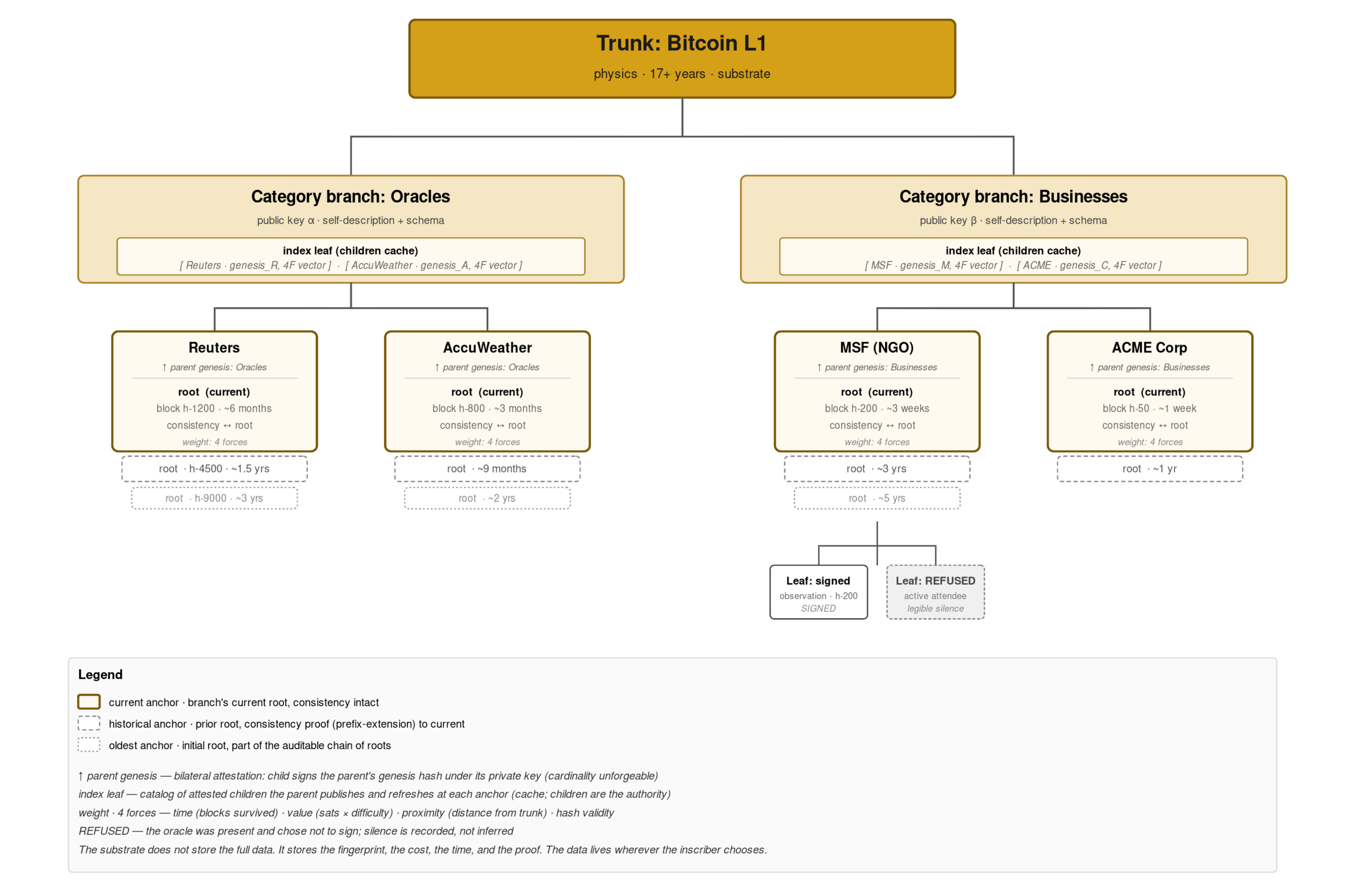
§6 The tree, at a glance
 {width=4.5in}
{width=4.5in}
The trunk is physics. Branches are identities. Sub-branches are categories of claim. Leaves are signed observations. Or, on an active-attendee node, recorded refusals. Vertical distance below the trunk corresponds to decreasing structural weight; horizontal breadth corresponds to accumulated history. The same geometry repeats at every zoom.
§7 Branches in time: the chain within the chain
A single anchor is a snapshot. A branch’s history is a different object, and reading it correctly matters.
An anchor is a pair: (root, block). The root is a Merkle hash of the branch’s state at the moment the root was computed. The block is the Bitcoin height at which the root was inscribed. The anchor vouches for exactly the leaves whose inclusion proof terminates at that root. No more, no less. A leaf added to the branch after the anchor’s block has no inclusion proof under that root, because the root was computed before the leaf existed. Not invalid. Just outside that particular snapshot.
A long-running branch is therefore a sequence, not a single object:
anchor_1 = (root_1, block_N1)
anchor_2 = (root_2, block_N2)
anchor_3 = (root_3, block_N3)
...
Each anchor commits the branch-state-as-of-its-block. A reader asking what did this body commit to as of date X walks to the nearest anchor at or before X and verifies against that root. What is new growth since anchor_k is the set of leaves present under root_{k+n} but not under root_k. The diff is trivially computable if the tree is append-only.
What makes append-only mechanically enforceable rather than merely declared is the consistency proof: a short cryptographic receipt that root_{k+1} is a prefix-extension of root_k. That the old leaves are still there, unchanged, and only new leaves were added. Without it, a branch’s operator could quietly drop an old leaf and re-root around the gap. With it, the prefix is stable. Certificate Transparency runs on exactly this pattern; it ports directly into the Tree of Proof.
For any leaf on a long-running branch there are three legible states, each read relative to a chosen anchor:
ANCHORED. Provable under at least one inscribed root.PENDING. Present in the branch’s local tree, not yet under an inscribed root.ABSENT. Not in any root, anchored or pending.
“New growth” is not a fourth state. It is a reader’s frame: a leaf anchored under a later anchor but not an earlier one. Change the anchor the question is posed from and the same leaf shifts. The architecture does not need a flag for “new.” It needs anchors and consistency proofs, and new becomes a query rather than a stored property.
The summary leaf. Reading a branch’s full tempo by walking every anchor and every root is possible but expensive. The fix is for the branch to publish a summary object. A structured leaf that lists, for every past anchor, the tuple (root, block, value_spent, leaf_count). The summary is itself inscribed under the branch’s key, under a root, at a block. It is a leaf whose content is the branch’s own index of itself.
The property this buys is trust-optional reading. A reader who trusts the summary reads the tempo in one round trip. A reader who does not takes each tuple and verifies it against Bitcoin directly. Finds the inscription at the block, confirms the root matches the summary’s claim. The audit is cheap per tuple and embarrassingly parallel across tuples. The summary is therefore a cache of facts the chain already recorded, not a new source of truth. A lie in the summary is mechanically detectable; the underlying chain data is always the authority.
Over time the branch publishes a sequence of summary leaves: summary_1, summary_2, summary_3, each inscribed at its own block, each an append-only extension of the prior, each carrying a consistency proof against the one before it. A branch thereby carries a chain of its own, nested inside the Bitcoin chain that guards it. The same recursion that produced the atomic Fingerprint produces the branch’s self-index. The tree is a chain of chains.
Three discipline lines worth holding.
First, keep the summary strictly structural. Each tuple is (root, block, value_spent, leaf_count) and nothing else. The moment the summary begins carrying the body’s self-description, who we are, why our inscriptions matter, the measurement layer has become a marketing layer, and the protocol’s cleanness erodes. Self-description belongs inside ordinary leaves, where a reader can weigh it in context. The summary measures. The leaves speak.
Second, the right to summarize a branch is not the branch’s alone. Because the underlying anchors are public, any third-party observer, an archivist, a mirror, a monitor, can compute and publish an independent summary of the same branch’s tempo, signed under their own key. A branch cannot monopolize the description of its own shape. External summaries cross-check internal ones. The substrate makes self-description auditable by default.
Third, branch cardinality at the parent layer, how many sub-branches a category branch holds, is not a self-reported integer in the parent’s summary. It is a count of children whose own genesis inscriptions name the parent’s genesis hash, signed under each child’s private key, anchored at each child’s own block. A parent claiming children that did not attest back has made an unenforceable claim, mechanically detectable by any reader who walks the children. The chain is the authority. The summary is the cache. The discipline holds at the parent layer the same way it holds at the leaf layer.
§8 Self-enforcement: the Nakamoto move, one layer up
Bitcoin holds without a custodian because miners have skin in the game. Attacking the chain destroys the value of the hash power they have already spent. The trunk is guarded by the private incentive of the parties with the most to lose from its failure.
The Tree of Proof inherits this property at every layer above the trunk.
A branch operator who has spent years inscribing anchors (paying sats, accruing tempo, publishing consistent summaries) has built a durable economic object. Breaking the branch, by quietly dropping a leaf, by rewriting a root, by publishing a summary that contradicts a prior summary, destroys the value of everything already accrued. The prior summaries are permanent. The contradiction is legible evidence. The cost of defection is not imposed externally. It equals whatever the branch has accumulated.
This incentive compounds on exactly the curve the weight compounds on. A one-year-old branch breaking its chain loses a year. A century-old order breaking its chain loses a century. The older the branch, the stronger the lock-in. The protocol does not need to enforce consistency. The branch operator enforces it, because the alternative destroys their own stake.
What generalizes from this is the architectural claim worth stating plainly: the architecture requires no external enforcement at any layer, because every layer carries the same game-theoretic property as the substrate. Bitcoin’s miners guard the trunk because of accrued hash power. Branch operators guard their own branches because of accrued tempo. Individual observers guard their own signatures because of accrued reputation under their public key. The move is Nakamoto’s, repeated at each level. Self-interest as the guard against defection, all the way up.
This is not a claim that the architecture is unbreakable. Any single branch can be abandoned, corrupted, or sold. What is claimed is weaker and more honest: breaking a branch is locally irrational for the party who built it, and the irrationality scales with the accrued time. There is no moment at which defection becomes cheaper than continuation. There is always a moment at which the accumulated weight exceeds any short-term gain from betrayal.
The architectural consequence is the one the book has been building toward: a substrate of memory that needs no custodian to remain honest, because dishonesty at any layer is punished by the layer itself. Structure guards structure. The reader can read.
§9 The seven seams
No architecture ships without open seams. Seven Seams names them. The short version, because an engineer reading this appendix deserves the warnings:
- I. Wealth bias survives hard money. Costly signals favor the party with more to spend. The filter is honest; it is not egalitarian.
- II. The trunk is abstract. Bitcoin is the trunk only by convention of reading. A fork, a social capture, a protocol ossification crisis would each re-open the question of what “the trunk” is.
- III. After money, who mines? If Bitcoin’s role drifts from monetary rail to epistemic substrate, the incentive for miners to keep the chain alive has to be re-derived.
- IV. The compass only works on agents that consult it. An AI that is not pointed at the tree does not gain anything from the tree’s existence.
- V. Weight is not meaning. A heavily anchored observation is not automatically a true observation. The four forces are necessary conditions for trustworthiness. They are not sufficient conditions for truth.
- VI. The timescale of rot. Branches that fall leave scars. A substrate that preserves those scars for centuries has not been built before. The long-run failure modes are not known.
- VII. The mirror has a gate. The tool that composed the argument is not reachable by most of the people the argument is for. Payment rails for the unbanked, argued into existence through infrastructure the unbanked cannot afford to use, inherit the access asymmetry of the infrastructure. The substrate does not solve its own reach.
A builder who starts here should expect to meet all seven on the path. Meeting them is part of building. Not meeting them is the mark that the build has not yet engaged with the hard problems.
§10 What to build first
The minimum viable fingerprinted oracle is smaller than the architecture. An engineer asking where do I start should start here:
- One oracle. One key. One category. A weather station. A bond-yield scraper. A local election tally. Any source the engineer already trusts, willing to publish under a public key they will not rotate.
- Daily inscription. One Merkle root per day, anchored via OpenTimestamps. Low throughput. High clarity. The goal is a year of commitments, not a minute of them.
- A public verifier. A static page that takes the public key, a date, and an observation, and returns
VERIFIED/REJECTED/ABSENT. No UI. No login. No admin. Just the check. - A second oracle, unrelated. The same category, different source, different key, same anchor schedule. Now convergence and divergence are locatable.
- A counter-commitment from a third party. Not a dispute mechanism. Just the demonstration that the substrate accommodates dissent in the same shape it accommodates agreement.
That is the seed. A year of this, two signed oracles, one counter-commitment, a public verifier, a growing set of recorded refusals, is the smallest instance from which the full architecture’s properties can be read off.
The rest is time.
What Already Exists
This is not a reason to wait.
The substrate has been running since January 2009. Block by block, tick by tick, the energy has been spent and the entropy has increased. The trunk is not waiting on a consortium, a standards body, a foundation, or a roadmap. It is already there.
The primitives are there too. Public-key signatures, Merkle trees, hash chains, timestamping, ordinal-style inscriptions, consistency proofs. None of them are conditional. Every component the architecture in these pages relies on is established technology, available to anyone with a keyboard and a connection.
Everything Part VI described (the fingerprint, the branch, the four forces, the hierarchy of weight, the legible silence, the consistency proof, the tree itself) composes from those primitives without asking permission from anyone. There is no protocol to invent. There is no chain to fork. There is no token to launch. Both have been running. Neither needs anyone’s blessing.
What is missing is not architecture. It is inscription. Someone, somewhere, has to take an observation, sign it under a key they will not rotate, hash the commitment, anchor the hash on chain. That is the act. The full datum behind the inscription (the underlying observation, the audit trail, the prose, the recording, the document) lives wherever the inscriber chooses. On Amazon. On a personal server. On a hard drive in a basement. On a USB stick in a drawer. The chain does not store the content and does not need to. It only holds the fingerprint, the cost, the time, the proof.
This reframes everything before it. The tree of proof, the fingerprint, the index problem, democracy for enemies, the bodies that believe, the seven seams, this sketch: none of it requires permission, funding, a consortium, a standards body, or a new chain. It requires someone to see what is already there and start inscribing.
The tree does not need to be built. It needs to be used.